Malware Analysis Quant: Phase 1 The Process - Securosis.
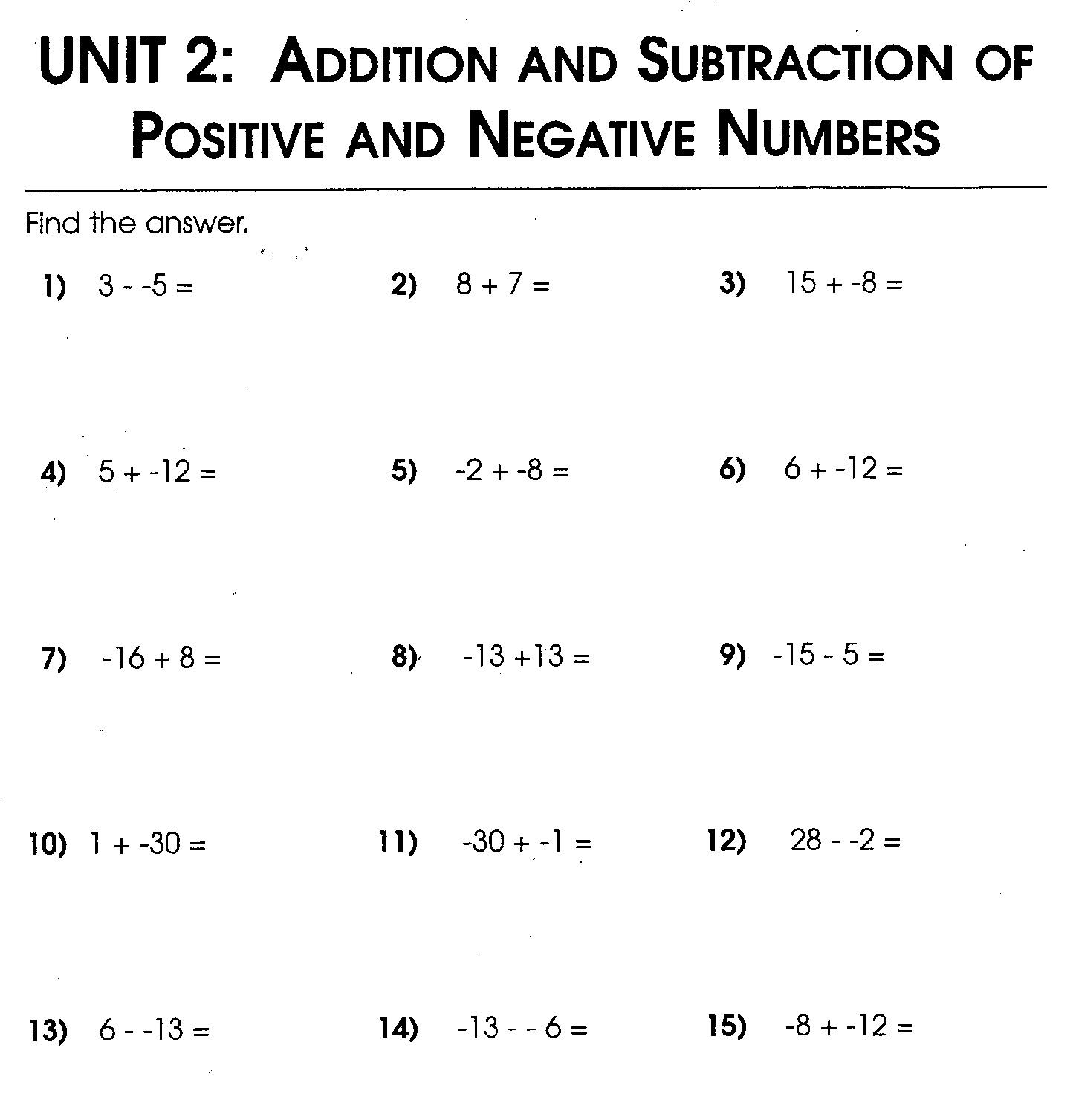
Malware analysis is the process of performing analysis of the malware and understanding its actions and behavior. It is of two types- static and dynamic analysis.
Our self-paced, online malware analysis training class provides an in-depth look into the world of malware and reverse engineering. Weaving complex methods with practical application, our training ensures the highest level of comprehension regarding identifying, isolating and defending against malware. Specifically, you'll learn how to perform dynamic and static analysis on all major files.
Conclusion. Running and analyzing malware using VMware and virtual machines involves the following steps: Start with a clean snapshot with no malware running on it. Transfer the malware to the virtual machine. Conduct your analysis on the virtual machine. Take your notes, screenshots, and data from the virtual machine and transfer it to the physical machine. Revert the virtual machine to the.
Malware, a shortened combination of the words malicious and software, is a catch-all term for any sort of software designed with malicious intent. Malware is sometimes called badware and is often used synonymously with many of the common types of malware, listed below.
The most confusing terminology is forensics. This term is associated to a location used for a specific form of judicial process. This terminology is related to the law which concentrates on scientific exams utilized in detecting crime. Experts utilize forensics to refer to the process of logging, gathering and auditing data (Daniel, 2012). This.
Graph visualization use cases: cyber security. 25th September, 2017 Andrew Disney. Our last blog post was the first of three exploring real world applications for graph visualization. Use cases for graph visualization: Cyber Security. Last time we reviewed two of the older commercial uses for graph visualization: law enforcement and fraud detection. We saw how, as data volumes grew, the.
About the Author: Emily Shawgo has recently graduated from Carnegie Mellon University with a master’s degree in Public Policy and Management with a concentration in Cybersecurity Management. She also has an undergraduate degree in Psychology and Political Science from Carlow University. Emily’s interests lie in penetration testing, threat analysis, and applying the study of human behavior.